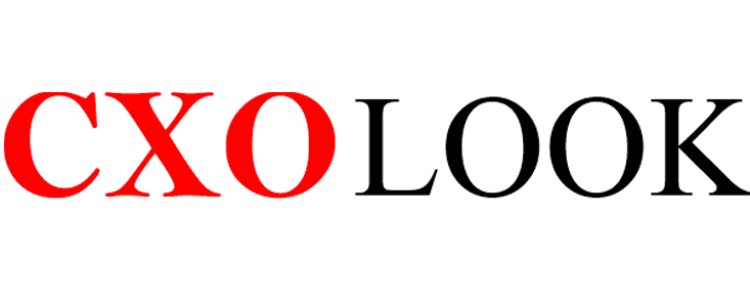
Cybersecurity is evolving rapidly, as never before, because of artificial intelligence (AI). According to a report by Arctic Wolf, “73% of businesses globally have included AI into their security operations, mostly to automate threat detection, response, and prevention.”
Protectors are depending more and more on AI to outperform adversaries as cyber threats get more complex. AI enables us to respond more quickly and accurately than legacy systems ever could, from real-time log analysis to predictive threat modeling.
In this article, we will provide a brief overview of the use of AI in cybersecurity, its key benefits, challenges along the journey, and key examples to understand its implementation.
AI in Cybersecurity: The Basic Concept
“AI in cybersecurity” means the use of AI technologies to improve security systems. These technologies enable automated threat identification, response, and prevention, including machine learning, neural networks, and data analytics.
AI can more successfully automate response actions by identifying patterns and anomalies that may point to a security concern through the analysis of enormous volumes of data.
The Key Benefits of AI in Cybersecurity
The increasing speed and sophistication of attackers, the expanding attack surfaces created by spreading networks, and the overwhelming volume of alerts that trap security teams in a loop of reactive defense are just a few of the compounding issues that defenders have faced for years.
It should not come as a surprise that more than 70% of security leaders have implemented or are assessing AI for their security operations to overcome these difficulties. The biggest benefit of AI in cybersecurity is its capacity for data input and summarization:
Security teams can react to cyber threats more quickly and precisely with the help of artificial intelligence, which has advantages like the following:
- Accelerated threat detection and investigation: AI can identify unusual patterns, correlate data, and provide quicker insights during incident response. Tools like EDR/XDR or SIEM may log thousands of potentially dangerous events.
- Improved alert prioritization and context: 83% of security teams report feeling overburdened by the volume of alerts, false positives, and a lack of context, and they are worn out from tracking down alerts from detection tools.
- By providing the context security teams require to make wise decisions, AI-enabled systems can assist in boosting the major alarms.
- The implementation of AI in cybersecurity provides users with a more in-depth understanding of threats. Besides, disparate cyber threat data can be combined and transformed into an actionable prioritizing model with the use of AI.
What are the Challenges of Implementing AI in Cybersecurity?
When implementing AI cybersecurity solutions, companies need to consider a number of risks and problems.
First, the cybercriminals that AI cybersecurity technology is intended to prevent may take benefit from it. Cybercriminals can change AI algorithms or introduce malicious content into AI data to undermine security measures. Additionally, they can employ AI to try to evade detection or identify and take advantage of weaknesses in an organization’s security systems.
Additionally, cybercriminals can develop more potent, complex, and focused cyberattacks using their own AI technologies. This involves implementing AI to produce deepfake images and videos, deceive workers into divulging private or confidential information, or breach an organization’s access restrictions and passwords.
Data privacy is another issue raised by the application of AI in cybersecurity. This covers things like the necessity of getting consent and maintaining transparency when gathering or utilizing personal data, the possibility of sensitive or private data being compromised, misused, or stolen, and the necessity for businesses to abide by pertinent laws and rules pertaining to user privacy, like the General Data Protection Regulation (GDPR).
Major Examples of AI in Cybersecurity
Organizations are already using AI in different ways to strengthen their cybersecurity posture. AI-powered malware detection systems that implement machine learning algorithms to detect, classify, and stop sophisticated malware threats that conventional anti-malware solutions could overlook are among the most inventive examples of AI in cybersecurity products and applications.
- Next-generation firewalls (NGFWs) powered by AI use the most recent threat intelligence to defend enterprises against both current and emerging cyberthreats.
- AI-based email and access controls stop phishing attempts by identifying and blocking phishing scams, tactics, and strategies through the analysis of email content, sender information, and email metadata.
- AI-powered behavioral analytics solutions that can track and examine network traffic and user behavior to spot unusual or illegal activity, spot possible insider threats or compromised accounts, and remove security issues.
- AI cloud security solutions that help businesses comply with cloud security standards, protect sensitive or private data stored in the cloud, and protect their cloud-based assets from theft, cyberattacks, and breaches.
- AI-backed endpoint security systems help businesses in protecting their networks and systems from ransomware, phishing scams, malware, and other specific assaults.
- Internet of Things (IoT) security solutions include AI capabilities to defend entire IoT networks and individual IoT devices against cyberattacks.
Bottom Line
AI has become a crucial component of the present cybersecurity landscape, providing better awareness, automated reaction capabilities, and better threat identification. Still, careful planning is vital for its successful implementation, such as maintaining data quality, integrating with current systems, encouraging human-AI collaboration, and upgrading models on a regular basis. Organizations can use AI to improve their security posture, reduce risks, and keep ahead of emerging cyberthreats by following the best practices.